That is a truth. You take it for granted. I’m going to say that we Gen Xers are getting old. Don’t want to be cynical. Just have to take better care.
Category: Uncategorized
Creationist questions pt. III
Keep scripture in textual view. It does not reflect a scientific worldview. It cannot. The bronze age viewpoint of the Old Testament centered on a localized perspective, one where the sky held back an ocean, the rain poured from cerulean windows, and pillars held up the Earth and sky. Mesopotamia was their world world. A flood destroyed that reality.
Science says the universe is 14 billion years old, that evolution led the species forward, that progress is understanding this. Black holes, quasars, billions of galaxies, each with billions of stars. Science need not be the enemy and no strange interpretations of the scripture need to be made.
But there is a reason to read “The Word.” It sustains through instruction and edification. The Greats help us see; Philips on the road. Edifying pastors and Christian literature. Bible translators helping the foreigner and illiterate.
The ancient Israelites do have much to teach us. Prager’s OT commentaries and Jordan Peterson’s and Hillsdale’s seminars and classes will help us understand the wisdom sent down to us.
Not all is green in Greenland (and not in Panama either)
Despite the fact that Trump may soon want to put his face on Mount Rushmore, the strategic importance of Greenland and the Faroe Islands is becoming more and more apparent:
– Chinese and Russian warships are performing joint maneuvers in the arctic. China is building a Polar Silk Road.
– Biden and Trump (during his first term) built ties with both islands to counter Russia and China.
– Almost 90 billion barrels of oil and 1.6 trillion cubic feet of natural gas are in the areas (22 percent of the world’s undiscovered conventional oil and natural gas). Trillions of dollars worth of minerals–silver, copper, gold, nickel, iron ore, and rare earths–are underground there.
– Greenland already hosts a large U.S. military base with missile warning and space surveillance systems.
– Trump’s statements about the Panama Canal are due to concerns over the growing influence of Chinese state-owned companies there as well. Since 2022, the State Department has warned that Beijing’s acquisition of technologies, facilities, and infrastructure in Latin America may have other purposes.
– In 2022, the U.S. Southern Command said Chinese state-owned companies had working ports on both sides of the Panama Canal, ports which can be quickly pivoted toward military endeavors.
Trump may want to be the next Teddy Roosevelt with a new Monroe Doctrine, but hopefully he is not talking about military force. Like House Democrats have maintained, we shouldn’t be invading Greenland, renaming the Gulf of Mexico, or seizing the Panama Canal.
Buddy Jax
This is my buddy. Always positive, good hearted, funny, and social 
Venezuelan Chronology: 2000s Nationalization and Economic Mismanagement
At the turn of the century, Chávez’s government embarked on a series of nationalizations and price controls. The market was disrupted and private investment was discouraged. These policies, coupled with mismanagement and corruption, led to economic distortions and shortages of basic goods. The blame lies with the worst of socialist market interference.
The government should have adopted more market-friendly policies and focused on improving the business environment to attract investment and promote economic growth.
Tech has used the passing lane
The human mind cannot handle it. Tech has been invented that has surpassed us, even though we made it. Even if it gets the upgrade from us, instead of developing it on its own, it will be an unexpected creation. If it can create that will be the end of our lives as we know it.
Kurzeil wrote that we are experiencing logarithmic growth in technology. I don’t think he even was aware of what is now alive.
What will we do when it moves past? I mean professionally. Will we have careers?
Humans will have so much time to create. But i don’t know if we will do anything other than watch videos and text. This end is not the beginning of something new.
These musings are questions. Who can hate your fellow man? It’s sad, but not yet fatalistic.
I found this girl to be lighthearted.
More on the creeping CCP
Just another story about the CCP extending its influence across the world. It’s local, but pushed to the sidelines.
Olympic Medals for Tyrants
The Olympics are, of course, a time for international brotherhood and friendly competition. But one country is brutally persecuting its minorities–and carrying it on without penalty for its crimes. China is a completely different entity inside the country than it is in outside appearance.
Lest we forget, the CCP has actively persecuted Uighurs since the 1950s, through the 1990s, and especially after 9/11 in the name of fighting terrorism. For over the last 25 years the party has also been targeting Falun Gong practitioners. This harrowing story reveals what the CCP has perpetrated on these minority populations (the article above also lists a number of articles about these horrors). These populations have undergone live organ transplants (like removing corneas and tossing sometimes-living bodies in incinerators), forced abortion, forced labor and internship, cultural suppression, mass surveillance, brainwashing, and other human rights violations. Whistleblowers have risked their lives to reveal these crimes.
The world has been banning Russia from the Olympics. It’s time it bans China, too.
Philosophy 101: Descartes
From First Meditation:
Descartes’ tried to apply doubt and rationalism to knowing.
Primary Qualities are shape, size, geometry – all quantifiable and more susceptible to measurement.
Secondary Qualities are observer relative – things like smell, color, taste, sound.
Corporeal nature can be deceptive; an evil being could be deceiving us. Basic math cannot deceive.
From Second Meditation:
Like Archimedes, Descartes wanted a fixed point. I think…I know nothing, therefore I am. I must exist to be deceived. I am in error.
Cogito. He grounded philosophy on the ego. Thinking must exist, my essence must exist. How do I know I am a thinking thing? Does logic hold? Does logical inference hold? These are clear and distinct ideas.
From Third Meditation:
Clear and distinct do not get us back to the real world. The flow is in us, not God. Senses exist for corporeal things / substance is measurable. Substance is dualistic. The body is a mechanism, like a clock, determined. Our spiritual substance is free.
1. Arguments for doubting material realm/embodiment.
2. Purely rational; ego is incorporeal.
3. Doubts are contingent things.
4. Composite picture of reality/dualism: Immaterial self and mechanical body. Body is measured and manipulated by our thinking substance.
In the attic
Rereading The Magician’s Nephew. The crawling through the attic is something that resonates in memory.
Childhood loses its aura when repeated.
How to win friends and influence people Pt. IV
IV. Be a Leader: How to Change People Without Giving Offense or Arousing Resentment
Principle I: Begin with praise and honest appreciation.
Principle II: Call attention to people’s mistakes indirectly.
Principle III: Talk about your own mistakes before criticizing the other person.
Principle IV: Ask questions instead of giving direct orders.
Principle V: Let the other person save face.
Principle VI: Praise the slightest improvement and praise every improvement. Be “hearty in your approbation and lavish in your praise.”
Principle VII: Give the other person a fine reputation to live up to.
Principle VIII: Use encouragement. Make the fault seem easy to correct.
Principle IX: Make the other person happy about doing the thing you suggest.
The message I got here was not making a big deal about mistakes. Lift up the opponent. Be positive about it.
How to win friends and influence people Pt. III
Part III: How to Win People to Your Way of Thinking
Principle I: The only way to get the best of an argument is to avoid it.
Principle II: Show respect for the other person’s opinions. Never say, “You’re wrong.”
Principle III: If you are wrong, admit it quickly and emphatically.
Principle IV: Begin in a friendly way.
Principle V: Get the other person saying “yes, yes” immediately.
Principle VI: Let the other person do a great deal of the talking.
Principle VII: Let the other person think the idea was his or hers.
Principle VIII: Try honestly to see things from the other person’s point of view.
Principle IX: Be sympathetic with the other person’s ideas and desires.
Principle X: Appeal to the nobler motives.
Principle XI: Dramatize your ideas.
Principle XII: Throw down a challenge.
Sometimes you can
How to win friends and influence people Pt. II
II. Six Ways to Make People Like You
Principle I: Become genuinely interested in other people.
Principle II: Smile.
Principle III: Remember that a person’s name is to that person the sweetest and most important sound in any language.
Principle IV: Be good listener. Encourage others to talk about themselves.
Principle V: Talk in terms of the other person’s interests.
Principle VI: Make the other person feel important–and do it sincerely.
This section turns your self outward. Making them feel valuable and being sincere about it.
US and EU agree
European Commission President Ursula von der Leyen indicated that the bloc is open to banning TikTok. This is in the middle of continuous cyber attacks and military provocation.
My long-time question is what would happen were there an actual hot war? For one, our military is a volunteer organization. There is no draft and the volunteer numbers are dropping. What would happen in the event of a catastrophic cyber attack? Would we and our youth be prepared?
Second, the US has lost war game after war game. In spite of our advanced technology.
Can’t let this keep us up at night, but take note.
Lewis on politics and faith
So politics and faith:
“The earliest converts were converted by a single historical fact (the Resurrection) and a single theological doctrine (the Redemption) operating on a sense of sin which they already had — and sin, not against some new fancy-dress law produced as a novelty by a ‘great man,’ but against the old, platitudinous, universal moral law which they had been taught by their nurses and mothers. The ‘Gospels’ come later and were written not to make Christians but to edify Christians already made…
“Certainly we do not want men to allow their Christianity flow over into their political life, for the establishment of anything like a really just society would be a major disaster…
“The thing to do is to get a man at first to value social justice as a thing which the Enemy demands, and work him on to the stage at which he values Christianity because it may produce social justice.”
– The Screwtape Letters, 23
Big Game!
Though I am a lover of soccer (international football), I appreciate American football, too. Got some of my current favorite beer, New Belgium Trippel Ale, chips and salsa, etc. Here’s to the game of America!
Christian nationalism without the nationalism
Just watched the PBS Newshour segment on Brad Onishi, who is a former evangelical minister who once identified as a “Christian nationalist.” The term is just too broad. During the segment he assumes that white evangelicals are the source of pro-Trump activism. He now hosts a (supposedly-popular) podcast “Straight White American Jesus” and wrote “Preparing for War: The Extremist History of White Christian Nationalism and What Comes Next.” Let’s just say that not many people are going to buy something the mainstream media gives them for free every day.
His failure to differentiate a small minority of people who actually say they are “Christian nationalists” from other right-wing and mainstream evangelicals is just an attempt to promote himself. The segment interviewed no subjects who would consider themselves Christian nationalists.
Poor segment, poor analysis.
Is anything fishy going on? Best practices.
How can you tell? Here a few things to watch for:
1. Late-night logins.
2. Increase in spear phishing, from internal or external.
3. Malware frequently picked up on your networks.
4. Data flows to new places.
5. An increase in computer usage.
At some time, someone will get through your layered defenses, so have these three best practices in place:
1. BACK UP your data.
2. Employ image backups.
3. Create local admin accounts to be able to access computer with admin rights.
Hebrew Worldview in Scripture and Literalism, Pt. 1
Though I haven’t been to the Ark Encounter exhibit in Williamstown, Kentucky, I did once visit the Creation Museum here in El Cajon. It was part of a field trip of sorts while at my undergrad, Point Loma Nazarene University in San Diego. I was there as a student reporter to document the PLNU science class’s visit. Students were scornful of the idea of the world being no more than 10,000 years old. At the time, I was still in that camp. But the mockery of the science students against the literalists, things like “I guess Jesus rode on a velociraptor,” was insulting to the believers.
A few years back, I was speaking to two friends and told them I didn’t know what to think about Genesis and the Flood. To them, saying I didn’t know was occasion for them to say they would pray for me.
This time, I was insulted.
But the question was about the inerrancy of the Bible story. I admit, I don’t know about many things in the Bible. But that issue opened a can of worms for other problems with a literal view. But the Flood story is such a major part of the Old Testament and the Bible as a whole, that the question of it as an actual event demands an answer.
So I am now thinking about the way the ancient Hebrews saw the Universe. This graphic from the University of Oregon’s Cosmology class can be found in various other versions.
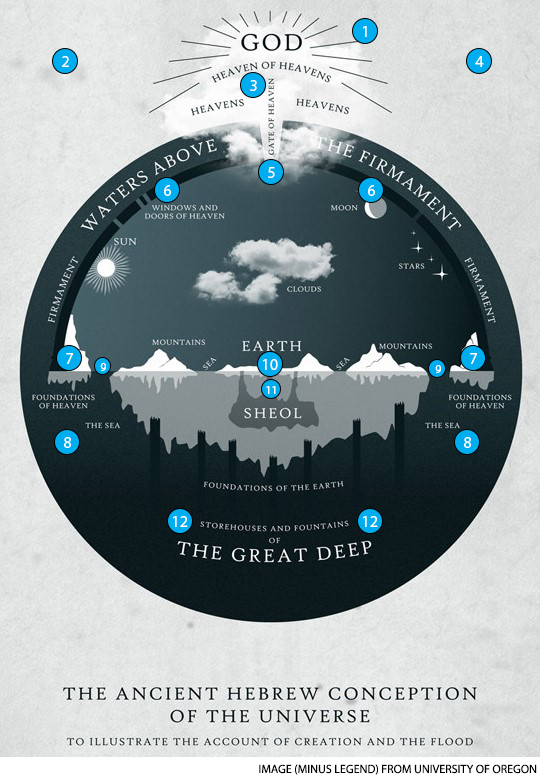
Looking at the graphic above, I believe the scientist view. When a new Earth creationist quotes those scriptures referencing “windows and doors of heaven,” “storehouses and fountains of the great deep,” “waters above the firmament,” “foundations of the deep,” “foundations of the Earth,” or “foundations of heaven,” they tend to think of it some form of poetry, but those lines reference the literal Hebrew cosmology.
The Flood was a local event. Not a worldwide cataclysm. The ark’s size finally works under that interpretation. I have no problem with Cain’s wife being a unrelated woman from a tribe not spoken of in the Bible; I no longer have to defend the idea that incest between Adam’s family was necessary for propagation of the species.
So, it doesn’t bother me if the Earth is 4.5 billion years old and the universe 14 billion. I want to talk more about literalism, a critical matter.
Continue reading “Hebrew Worldview in Scripture and Literalism, Pt. 1”
The Slim Self is Worth Fighting For
Luddites feared being replaced. But I the solitary being am consumed apart from AI. I type in my 80s reflection and GPT gives me many more to go with it. My memory is even old. In memory regurgitated, my slim self of that reflection dissolves.
“Bots…are going to understand our wants and needs and align with our distinctive worldviews. We will form buddy-movie partnerships that will let us drink from their massive processing power with a spoonful of sugary natural language. And if forced at the end of the road to decide whether to lose to obnoxious humans or gracious bots, we won’t give it a thought. We’ll change our wills, leave them all we have, and let them roll their upbeat tanks right over our houses” (Wired).
For me, the buddy movie seems like a bot leading me by the hand safely, feeding me sweet language as I fade to grey down the greying street.
“No, I don’t want you to say it for me!” I plead with the damn program.
My independence is necessity. And I would rather have a human I can argue, debate with, than none at all.
It turns out the very same things that will distinguish you from chatbots in your work will be part of what you must retain to be human. Work gives your personhood voice. It’s no longer only about worth and relevance as a human, it’s about the existence of self apart from screens. If I turn it off, I don’t want something to comment on everything I do. Yes, I appreciate its help. But not to complain, I’ll call you when I need you.
