Out and about this app finds safe spots:
https://www.wifimap.io
For other services, devices, power plants, mobile phones, refrigerators and Minecraft servers: https://www.shodan.io/
Out and about this app finds safe spots:
https://www.wifimap.io
For other services, devices, power plants, mobile phones, refrigerators and Minecraft servers: https://www.shodan.io/
If you’re hit by ransomware, do not panic. Think through the processes below.
1. When can you start on your client’s recovery? At least seven days will lapse before you can get to work on the systems.
2. How long will my client be down? Give your client some ready, loaner servers.
3. Should my client pay the ransom? Keep your client asset list ready. What is the priority for bringing the data back online.
4. Am I as an MSP going to be liable? You will encounter this later in the process. Make whoever provides your errors and omissions insurance aware of the problem.
5. How do I prevent this?
– Set up users so they don’t have admin rights.
– Do not log in to workstations with domain admin accounts.
– Create an alert to let you know if you have a domain admin logged into a machine that’s been idle for more than an hour.
– Don’t give normal users domain access rights. Only give them these rights when they are applying updates. Give them local admin rights only as needed and create these rights on a separate account.
– Do not share passwords or usernames between accounts.
– Never log in to your backup servers or solution from the servers you are backing up.
– Check your AV status, running or not? Make sure it gets updated and users can touch it.
*** Ransomware doesn’t work if it doesn’t kill the backups. ***
I can’t do any better than to point out that Google incognito mode shares your IP address, device data, and browser history despite seemingly offering a private browsing experience. “Google has updated its disclaimer in Incognito Mode according to MSPowerUser, and lawyers have been working to finalize a settlement.”
Read for more.
That was one of the famous lines from Sneakers (1992). Today, you may have devices and apps listening in on your passport. Voice assistants like Bixby, Siri, or Alexa may be doing it. Apple says Siri runs a speech recognizer at all times. “Hey Siri” or “OK Google” can start the recording. Apps may also be recording your voice.
Use these recommended steps to protect yourself.
1. Turn off Siri, Bixby, or Alexa.
2. Turn off your microphone by going to the settings for each app that may use your voice (or ambient sound!).
3. Use anti-malware software.
4. Use a VPN.
Anti-virus software may help you. Just like a VPN can.
Doing a piece on technical debt and cybersecurity. Developers know the term technical debt. When faced with a deadline, peripheral requirements are sacrificed for expediency. The proper course of action is to spend more time to complete a project. Sacrifices cause the solution to deviate and, in the long term, can impact performance, scalability, resilience, or other similar system characteristics.
While not all technical debt can result in negative outcomes, shortcuts, and outdated security and infrastructure can impact your cybersecurity significantly. Not only can efficiency be reduced, but an easy and limited solution can amount to an open door. The organization’s eyes are not on the future and the door gets wider.
In short, you need to do the job right, including modernizing old tech and configuring correctly. You must also adapt to the changing cyber landscape–or increase your vulnerabilities by not doing the job properly.
So your living room may still have wrapping paper on the floor and it was easy to unwrap those gifts and forget to set them up correctly. Use the following settings and practices to make your new gadgets run privately and securely:
These are indispensable actions. I hope you had a great Christmas!
Some basic cyber practices for the holiday!
So, the spirit of Christmas and Hannukah is here: houses and trees lit up, gift wrapping — and scammers. The denizens of the underworld may ruin your holiday while you are concentrating on shopping and giving. They even steal from charitable givers. Continue reading “All I Want For Christmas Is Not To Be Scammed”
Bug bounties are to the internet what wanted posters were to the Wild West. Companies like Google, Facebook, Microsoft, and government offices like the U.S. Department of Defense have been enlisting professional “white hats” (also “ethical hackers” or “security researchers,” sometimes “penetration testers”) to find weaknesses in their defenses — with hefty cash rewards for those who find them (see appendix at end).
White hats – the guardians of cybersecurity — help you find the vulnerabilities in your systems and networks before the black hats do. If a malicious user compromises your network, you may not know for 60 months. That’s the average time until a business becomes aware that a hacker has been in its network. And many serious problems for your business can occur during and after that time. While big companies like Equifax, Maersk, and Target have become victims of cyberattacks and recovered, small to medium-sized businesses hit by hackers may not survive. SMBs may not have the necessary resources and staff to recover fully. Continue reading “Seeing Signs of Network Compromise? The Guardians of Cybersecurity Can Help”
Unsubscribing from email lists can be a door-in for malicious email listers. It’s better to use Gmail or your email provider’s block feature. Choose block as spam. Auto unenroll.
This 23andMe data breach came out last Friday, but I wanted to mention it. It didn’t get the notice it should have because of Saturday’s events. It is certainly odd that Jewish and Chinese individuals were targeted. Why anyone would want this type of data, from a certain ethnic group?
But speculation aside, this is a big deal. The culprits are selling these records.
Just a reminder for recognizing fake flash media (SSDs and USB flash drives), since I shopped for some recently.
OK I admit it. I look for bargains online that are not smart purchases, e.g. USB flash drives or solid state drives (SSDs) that are cheap. But those bargains may be hiding garbage technology or malicious software. In general, you should buy for the quality and dependability of a known manufacturer (see suggested manufacturers below). Also consider whether you want a lower or higher range drive from these companies as price will vary. Continue reading “Beware Fake USB Flash Drives and SSDs”
Had a friend who had three of these attacks. Always be wary of messages from friends
https://cyberguy.com/scams/this-facebook-messenger-phishing-scam-is-stealing-millions-of-passwords
I use Norton/Lifelock and they’ve put out this cool little AI-powered site (https://us.norton.com/products/genie-scam-detector) and app (https://apps.apple.com/us/app/norton-genie-ai-scam-detector/id6448706515), which will tell you if the text or image your upload is suspicious. You can upload a screencap of a message, social post, or other site. When you interact with Genie, you can learn if you have encountered a scam or malicious message. Some training still needed; it’s in early access right now, but will no doubt improve.
Understandably, companies and organizations are embracing zero trust with the daily business pressures that have evolved over the last few years. The pandemic presented small businesses and organizations with new security considerations: remote workers with access to a much wider range of apps, new ways of working onsite, bring your own devices, cloud-based assets, and new supply chain and vendor processes. Furthermore, you may have added these changes to your network ad hoc. Now, you have an unwieldy patchwork of devices and computers at your business. Continue reading “Safeguarding Customer Trust and Compliance: Why Organizations Are Embracing Zero Trust”
 This is a pretty cool tool.
This is a pretty cool tool.
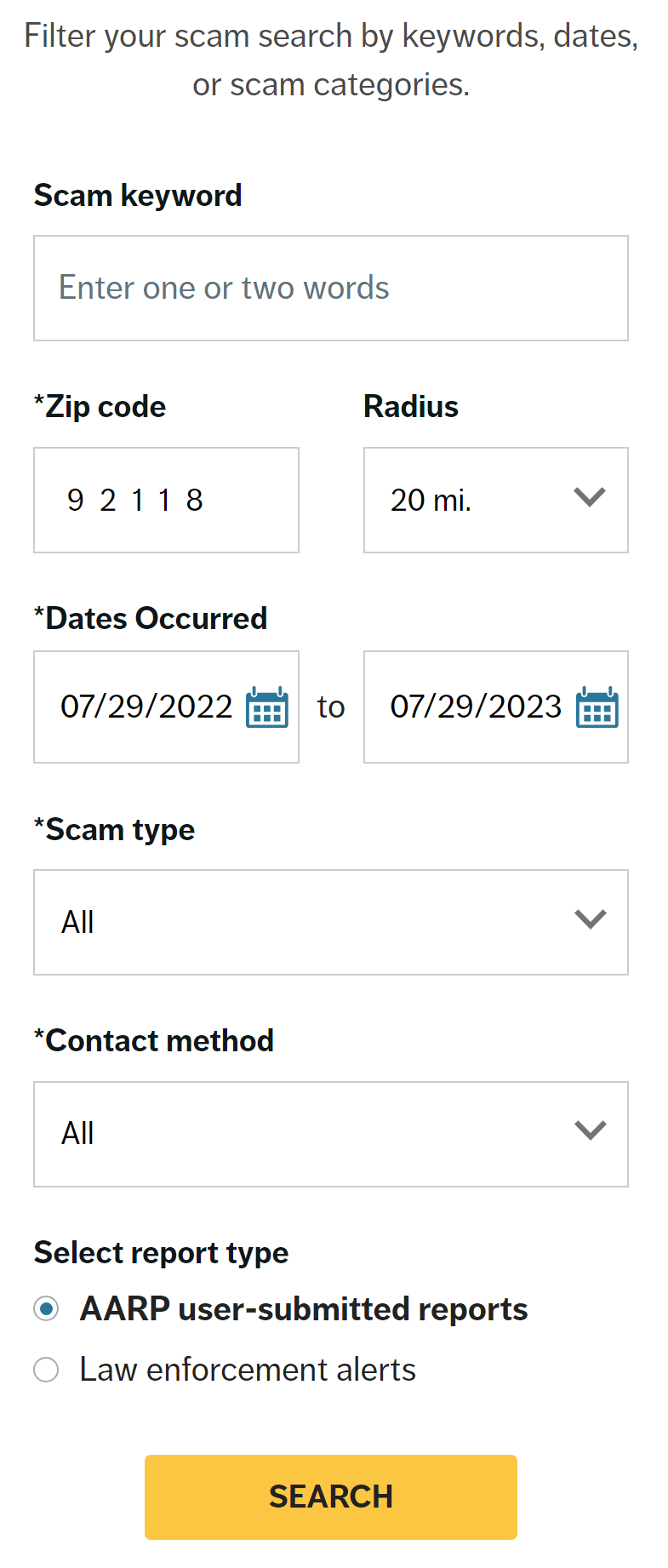
https://www.aarp.org/money/scams-fraud/tracking-map.html
You can search by scam keywords used, zip/location, type of scam, dates, or type of contact, or if the alert was from AARP users or law enforcement.
Similarly, the FTC’s Consumer Sentinel Network has this tool: https://public.tableau.com/app/profile/federal.trade.commission/viz/FraudandIDTheftMaps/FraudbyMetroArea
Over 50% of enterprise routers are not cleared of data before reselling them. This includes sensitive information like login credentials. Make sure your router creds are not out on the dark web, vulnerable to reuse.
The first thing you should do when starting a new cyber position is an inventory of networking and computer assets. But this also should be an ongoing practice. What is not known becomes an attack vector. Then you’ll be the smart guy. Save yourself from embarrassment…and worse.
Just wanted to touch on one scam that is making the rounds. Many users know the scams to do with sending money to anyone over the internet. But what if you are given a check from a potential employer, such as to buy equipment or work tools, to deposit? What could happen? I interviewed a Chase representative, who told me that he has had recent cases where someone would deposit the check and then the scammer would tell the victim to send on part of the money, or buy gift cards with it. Similarly, “reshipping scams” will ask you to send on a package or funds to another address.
Another such scam can make use of your bank tracking number.
From the FTC’s Consumer Advice:
“The check will bounce, and the bank will want you to repay the amount of the fake check.”
Another warning here is a request to send ID such as a driver’s license as part of pre-employment requirements.
It all goes to the age-old maxim “if it’s too good to be true, it probably is.”
It used to be that antivirus tools focused on Trojans, worms, and viruses. This AV software relied on strong signature-based detection and regularly-updated signatures. Newer AV software has added behavior-based protection against unknown threats.
Antimalware software now also focuses on exploit tools and off-the-cyber-shelf software used by malicious long-term threat actors (Advanced Persistent Threats) to maintain access over time and continue their exploit.
Utilities and infrastructure, government agencies, hospitals and healthcare institutions, schools, food production and distribution industries–even ferry service to Martha’s Vineyard, all have been attacked by cybercriminals using ransomware, probably now the most used kind of exploit of network systems.
“Even as we speak there are thousands of attacks on all aspects of the energy sector and the private sector generally…it’s happening all the time,” said Energy Secretary Jennifer Granholm to CNN. Continue reading “Ransomware Timeline”